By Ayaskant Das
New Delhi: Chinese Communist Party (CCP) and its People’s Liberation Army (PLA) use data collected about Indians, and in the future through mobile 5G networks, as a weapon and these technologies are clearly a spying tool for India‘s northern neighbour, according to experts and thinkers on India’s national security.
They also called for a long-term strategy to provide greater impetus to development of indigenous technologies and manufacturing capabilities in the telecom sphere, apart from an omnibus national security law to deal with non-military threats from the Asian dragon.
There also exists a need to curb China‘s economic expansionism, based on its reliance on manufacturing cheap goods coupled with CCP government’s subsidy, which has almost de-industrialised the United States and several European countries.
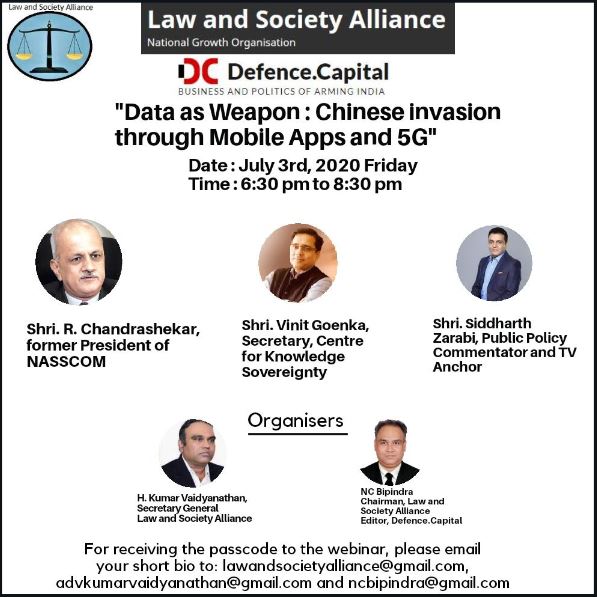
The experts and thinkers at the webinar on “Data as a weapon: Chinese invasion through Mobile Apps, 5G” were India’s retired Telecom Secretary and former NASSCOM president R. Chandrashekhar, data sovereignty activist and Centre for Knowledge Sovereignty Secretary Vinit Goenka, and senior journalist and television news anchor Siddharth Zarabi. The webinar was hosted on June 3 by New Delhi-headquartered think-tank Law and Society Alliance and defence and strategic affairs news magazine Defence.Capital.
“A long-term strategy aimed at providing greater impetus to development of indigenous manufacturing industries along with an omnibus national security law to deal with threats outside military issues are essential for taming the Chinese dragon that has built its global economic clout by amassing data from across various countries,” the experts said.
The webinar happened just days after India banned 59 Chinese mobile Apps and is barring Chinese companies from participating in Indian infrastructure projects such as national highways, railways and other critical sectors, even as their armies are engaged in an eyeball-to-eyeball confrontation in eastern Ladakh for the last two months.
Vinit Goenka, in his forceful argument for data sovereignty, said the ban of 59 Chinese mobile apps was just the tip of the iceberg, as the Asian dragon gobbles up massive amounts of data and indulges in digital colonisation of India by capturing the online activities of Indians.

China surreptitiously pilfers data through common household devices like Closed Circuit Television (CCTV) cameras, most of which are either imported from China or assembled in India with Chinese components because of the affordability factor. The sensors in these devices can be controlled directly from the Chinese territory, as has been experienced globally in several security breaches that have happened in the recent years, he said.
“The data helps China and its military operators of the Chinese companies to do data mining of its mobile apps users through quantum computing. A mobile app like TikTok was used to penetrate the untapped Indian rural market by allowing use of local languages, while American apps such as Facebook still relied on English language,” Goenka said.
“Data mining also helps China to assess what cheap goods to manufacture and where in India to dump those goods to influence buyer behaviour, thereby killing local manufacturers and traders dealing with those goods. He gave examples of how items used in religious ceremonies by Indians were manufactured by China and dumped in areas where such rituals are performed, killing the local businesses. The need is for data sovereignty, which should remain solely within political boundaries,” he said.
While social media has become extremely popular and pervasive in the 21st century, where a lot of data has moved on to gargantuan platforms like Facebook, Twitter and TikTok, a long-term strategy beyond banning of Apps is needed in India to deal with the challenges posed by the changed nature of relationship between security and economic issues. Data collated through the platforms is used for value addition by the host country through analysis and inference with the use of artificial intelligence and machine learning, Goenka added.
Chandrasekhar, who has served both in the government and in the industry body for the telecom and information technology sectors, said data is used by the platforms to alter and influence human behaviour besides pushing public opinion. This has happened over the last few years and influencing public opinion in an enemy country is such a huge weapon in the hands of China and could change political fortunes of political parties and leaders in a democracy.

“With Chinese Apps and 5G technology, there have been allegations of their links to the People’s Liberation Army and the Chinese Communist Party government. India cannot afford vulnerability form China now that India is on the brink of an armed confrontation at the borders. The ultimate solution lies in developing our own capabilities and capacities in the critical sectors such as telecom, communication and information technologies that also have defence and military applications. The only approach to weaponisation of the social media and the communication technologies by China is to build domestic capability as early as possible,” Chandrashekhar said.
The former bureaucrat, with a lot of insider knowledge and technical wisdom, said with 5G technology, data exchange takes place over telecom networks. “Unless our telecom networking infrastructure is secured, we won’t be able to face the challenge posed by China. In order to secure data sovereignty, public sector units in India including Centre for Development of Telematics (C-DOT) and Centre for Development of Advanced Computing (C-DAC) have to play a more defining role in the area in the future.”
China’s philosophy in supporting companies, such as Huawei and ZTE Corporation, for their 5G technology and TikTok and others engaged in running social networking platforms, is to create modern-day versions of the East India Company, which had been used by the British to colonise India, he said.
Siddharth Zarabi, with over two decades of experience covering Indian public policy and business, said India should look up to the United States for its omnibus national security law and develop its own legislation in national interest.

“India’s composition of its trade with China can be reversed. The US has done so citing security issues despite being a signatory to the World Trade Organisation. The government should follow the ‘Atma Nirbarta‘ (self-reliance) model, as has been stressed upon by Prime Minister Narendra Modi. For several years now, the focus on ‘Swadeshi‘ (loosely translated as ‘indigenous’ and ‘make in India’) had been compromised. National sovereignty cannot be mortgaged by politics,” Zarabi said.
He said in 1999, the Pakistan Army ingress in Kargil forced India to think about how strategic spots on the borders cannot be ceded and domestic military strength is imperative. Chinese aggression in 2020 has awakened the 130 crore Indians to the threat posed by digital colonisation and how, it is important for India to not only build its military and economic strength, but also develop strategic alliances with like-minded nations globally to counter China.
There was consensus among the panelists that in a post-COVID world order, India has to be careful about the message it sends out in its bid to protect its sovereignty from Chinese invasion in the digital and commercial space.
The session was moderated by Law and Society Alliance chairman and Defence.Capital editor N. C. Bipindra and a vote of thanks was proposed by Law and Society Alliance secretary-general H. Kumar Vaidyanathan, a Mumbai-based law practitioner.
